Your Phone Can Be Tracked – And It’s Easier Than You Think
Most of us carry our phones everywhere, trusting them with everything from passwords to private business conversations. But here’s the unsettling truth: phone tracking is far more common – and easier – than most people realize. Whether it’s a jealous partner, a disgruntled employee or a cybercriminal targeting your business, anyone with the right tools […]
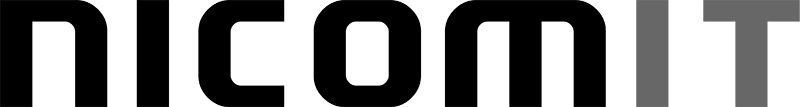
The Compliance Blind Spot: What You’re Missing Could Cost You Thousands
Many small business owners still think regulatory compliance is only something big corporations have to worry about. In 2025, that’s no longer true. With tighter rules around privacy, cybersecurity, and data handling, small businesses across Canada are under more scrutiny than ever—and the risks of ignoring compliance are bigger than most realize. Request Your FREE […]
The Hidden Cost Of “Cheap” IT
You know the saying: You get what you pay for. And nowhere is that more obvious than in IT. On the surface, a cheaper managed IT services agreement might seem like a win: lower monthly costs, basic support, maybe even some cybersecurity tools thrown in. But dig a little deeper, and you’ll often find hidden […]
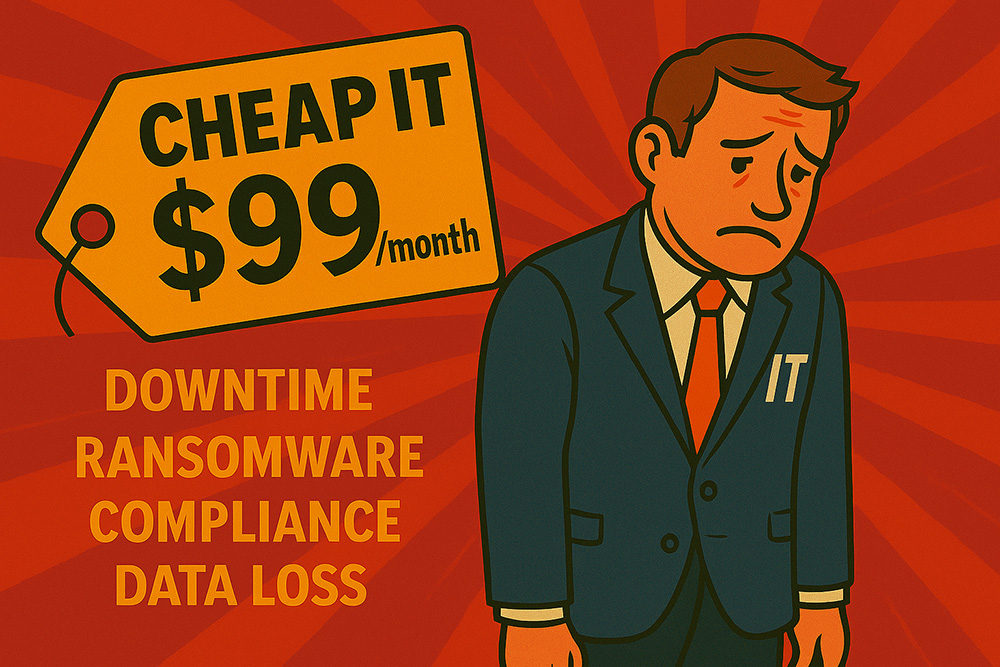
The Hidden Costs Of Waiting: Why You Can’t Afford To Delay Your Windows 10 Upgrade
Windows 10 hits end-of-life in October 2025, and putting off the upgrade could cost you more than just an IT headache. From security risks and software issues to emergency expenses and compliance violations, waiting comes with real consequences. Here’s why acting now is smarter – and cheaper – than scrambling later. Request Your Network Assessment […]
7 Questions You Should Be Asking Your IT Provider Every Quarter (But Probably Aren’t)

If the only time you talk to your IT provider is when something breaks – or once a year at contract renewal – you’re missing critical conversations. Your tech setup needs regular check-ins, not just emergency calls. These seven questions will help you stay secure, productive, and ahead of problems before they cost you. Request […]
Out Of Office, Out Of Luck: What Happens When Your IT Breaks While Everyone’s On Vacation?

It’s summer. Your team’s scattered, your IT person’s on vacation—and then something breaks. Systems go down, files vanish, and there’s no one to fix it. This post explains why reactive IT falls apart when you need it most, and how a proactive approach keeps your business running, even when everyone’s out of office. Request Your […]
Shadow IT: How Employees Using Unauthorized Apps Could Be Putting Your Business At Risk

Shadow IT – apps and tools employees use without IT approval – is one of the fastest-growing cybersecurity risks in business today. These well-intentioned shortcuts can lead to data breaches, compliance issues, and major vulnerabilities your IT team can’t see coming. Request Your FREE IT Optimization Plan Today Your employees might be the biggest cybersecurity […]
Is Your Printer The Biggest Security Threat In Your Office?

Your office printer might seem harmless – but it could be one of the biggest security risks hiding in your network. Request Your Network Assessment Today If I asked you to name the biggest cybersecurity threats in your office, you’d probably say phishing emails, malware, or weak passwords. But what if I told you that […]
The Fake Vacation E-mail That Could Drain Your Bank Account

Planning a vacation this year? Make sure your confirmation e-mail is legit BEFORE you click anything! Request Your Network Assessment Today That’s right, summer is right around the corner and cybercriminals are exploiting travel season by sending fake booking confirmations that look nearly identical to emails from airlines, hotels, and travel agencies. These scams are designed to […]
The Biggest Mistakes We See Business Owners Making In IT and Cybersecurity
A client recently asked us, “What mistakes do you see business owners making the most when it comes to IT and cybersecurity?” Oh, where to begin… Request Your IT Optimization Plan After years of working with businesses of all sizes, the biggest mistake we see time and again is treating IT and cybersecurity as an afterthought. It […]