April Fools Jokes Are Over, but These Scams Aren’t Fun Pranks
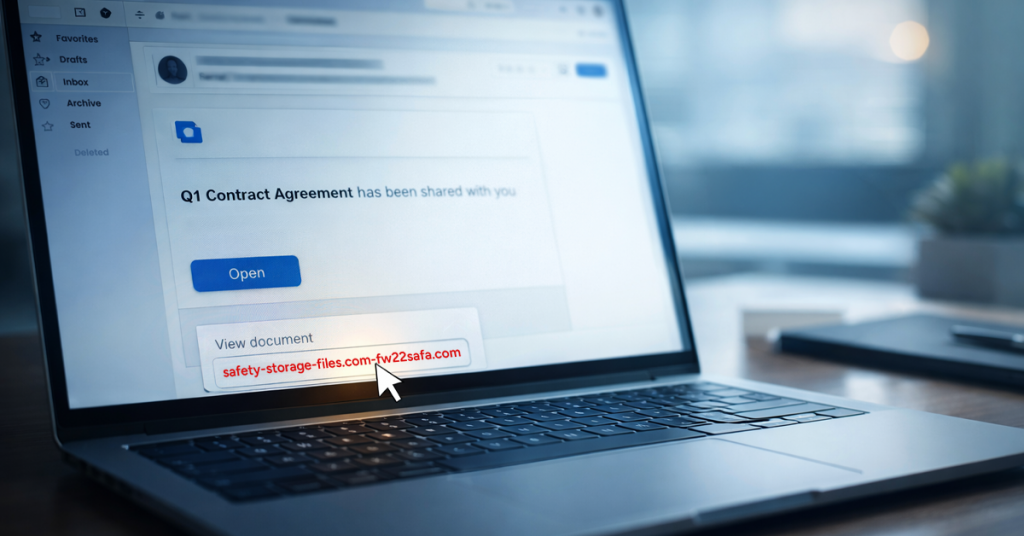
Spring is one of the most productive seasons for hackers. Not because teams are careless, but because everyone’s busy, a little distracted and moving fast.
Spring cleaning usually brings to mind closets and storage rooms, but for most businesses, the real clutter goes well beyond what’s on a shelf. It shows up in old laptops tucked away in drawers, retired printers in the back office, backup drives from years ago and boxes of cables no one wants to throw out just in case.
None of this is unusual. Every business accumulates it over time. The difference is whether there’s a clear plan for what stays, what goes and how to handle the rest before it quietly becomes a risk instead of just clutter.
When you buy new equipment, there’s usually a clear reason. It’s faster. More secure. More capable. It supports growth.
Most businesses plan how they buy technology. Few plan how they retire it.
When you retire equipment, it often happens quietly. A device gets replaced. It gets set aside. Eventually, someone decides to clear space.
That’s normal.
What’s less common is treating the retirement of technology with the same intention as the purchase.
Old tech still has usable value, recyclable components, and stored access or data. Sometimes it creates operational drag if it’s just sitting around taking up space and attention.
Spring is a natural time to step back and ask: What’s still serving us and what’s just taking up space?
What are we actually retiring? Laptops? Phones? Printers? Network gear? External drives? You can’t manage what you haven’t identified, and a quick walkthrough often reveals more than expected.
Every device typically falls into one of three categories: reuse (internally or through donation), recycle (through certified e-waste programs) or destroy (when data sensitivity requires it). The key is making the decision intentionally rather than letting hardware drift into storage purgatory.
This is where a little discipline goes a long way.
If the device is being reused or donated, remove it from your device management systems, revoke user access and verify data wiping (not just a factory reset). When you delete files or do a quick format, the data doesn’t disappear. The computer just stops keeping track of where it’s stored.
A study by data security firm Blancco found that 42% of resold drives purchased on eBay still contained sensitive data, including personal tax records and passport information. Every seller claimed the drives had been properly wiped. A certified data erasure tool overwrites every sector and gives you a verification report.
If it’s being recycled, use a certified e-waste provider, not the dumpster or the curb. One thing worth knowing: Best Buy’s popular recycling program is for household residents only, not businesses.
For commercial equipment, you’ll need a certified IT asset disposition (ITAD) provider or a business-focused e-waste recycler. Look for providers with e-Stewards or R2 certification (both have searchable directories at e-stewards.org and sustainableelectronics.org). Your IT provider can typically coordinate this as well.
If the equipment is to be destroyed, use certified wiping or physical drive destruction (professional shredding or degaussing), and keep a record: device serial number, method used, date and who handled it.
This isn’t about paranoia. It’s about closing the loop properly.
Laptops usually get attention. Other equipment often doesn’t.
Phones and tablets may still contain email access, contact lists or authentication apps. A factory reset handles most of it, but for business devices, a certified mobile wipe tool is more thorough. Apple, Samsung and most major manufacturers offer trade-in programs, even for older devices, so you may get credit toward new equipment.
Modern printers and copiers frequently include internal hard drives that store copies of everything they’ve ever printed, scanned, copied or faxed. If you’re returning a leased copier, confirm in writing that the hard drive will be wiped or removed before the machine is redeployed.
Batteries Batteries are classified as hazardous waste in Canada and shouldn’t be thrown in the regular trash. Requirements vary by province, but for businesses, proper disposal isn’t optional. Remove batteries from devices when possible, tape the terminals to prevent short circuits and bring them to a certified drop-off location. Programs like Call2Recycle have searchable maps of approved sites across Canada, and retailers such as Staples, Home Depot and Lowe’s accept rechargeable batteries at many locations.
External drives and retired servers tend to live in closets longer than planned. None of these are automatically problems, but they deserve the same retirement process as everything else.
Spring cleaning isn’t about getting rid of things. It’s about making space.
Clearing out outdated equipment is one piece of the picture. But while you’re stepping back and evaluating hardware, it’s worth asking a larger question: Is our technology supporting how we want to run this business?
Hardware comes and goes. Today, it’s software, systems, automation and process design that really drive productivity and profitability.
Retiring old equipment properly is good housekeeping. Ensuring the rest of your technology aligns with your goals keeps you moving forward.
If you already have a clear process for retiring equipment, great. That’s exactly how this should feel: simple and routine.
But while you’re thinking about replacing old hardware the right way, it’s also a good time to review the bigger picture. Are your systems streamlined? Are your tools working together? Is your technology helping you grow or just keeping the lights on?
If you’d like to take a step back and review how your tech stack, systems and processes are supporting your productivity and profitability, we’re happy to have that conversation.
No equipment checklist. No hard sell. Just a practical discussion about how technology can work better for your business.
And if this sparked an idea for another business owner, feel free to pass it along.
Spring cleaning shouldn’t stop at closets. It should include the systems that keep your business running.
If you’re already handling equipment the right way, this is the next step. Let’s look at how your systems and tools are working together and where they might be holding you back. No checklist. No pressure. Just a practical conversation.
If this made you think of another business owner, feel free to pass it along.

Complete this form to get started and we will contact you to discuss the next steps. Or call us at 1-833-231-6182 to get started.
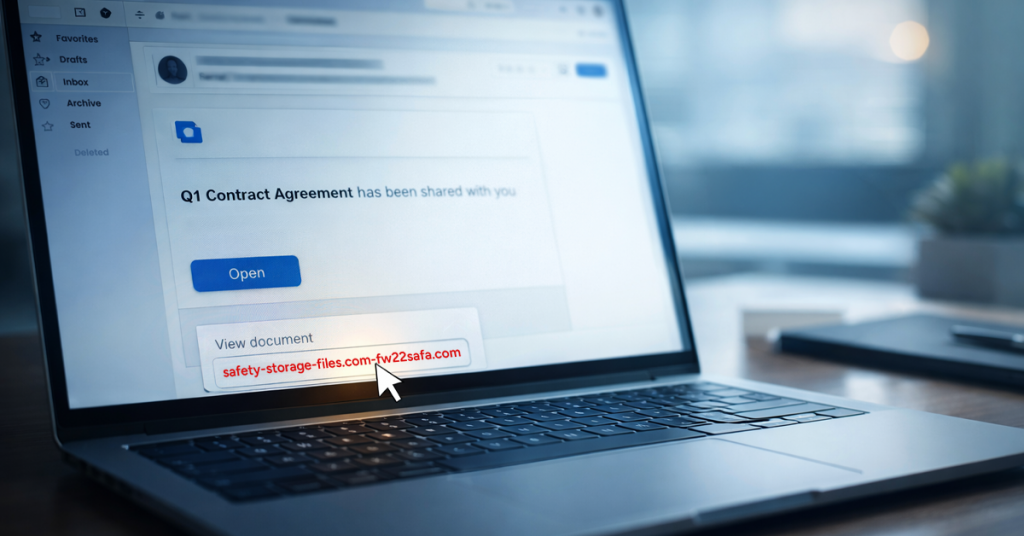
Spring is one of the most productive seasons for hackers. Not because teams are careless, but because everyone’s busy, a little distracted and moving fast.

A powerful iPhone hacking toolkit is now publicly available to any cybercriminal with an internet connection. If your employees haven’t updated their iPhones recently, their
For a split second, time slows as you watch coffee spill across the keyboard and seep into places it was never meant to go. The